Sites.Selected permissions are required for the non-interactive application to get access to a specific SharePoint site using Microsoft Graph API and/or SharePoint API.
Below are the steps to get access to SharePoint site with Sites.Selected API permissions:
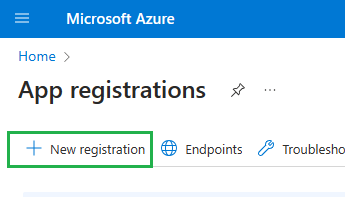
1. Register an application in Azure (via Azure portal GUI, PowerShell script or helpdesk/servicedesk request), e.g. with GUI you’d login to portal.azure.com,
the search for “App registrations” and select “+ New registration”:
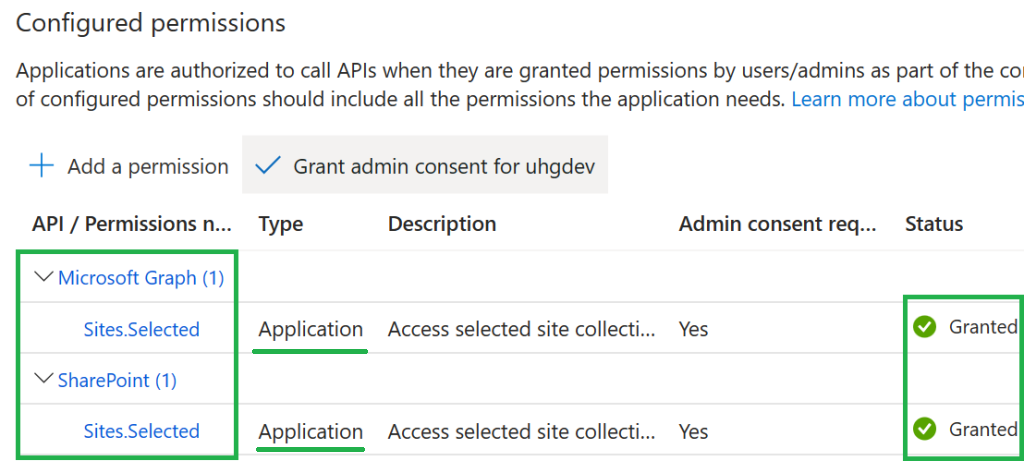
2. Update the app “API permissions” – so both – MS Graph API Sites.Selected and SharePoint Sites.Selected application API permissions are configured:
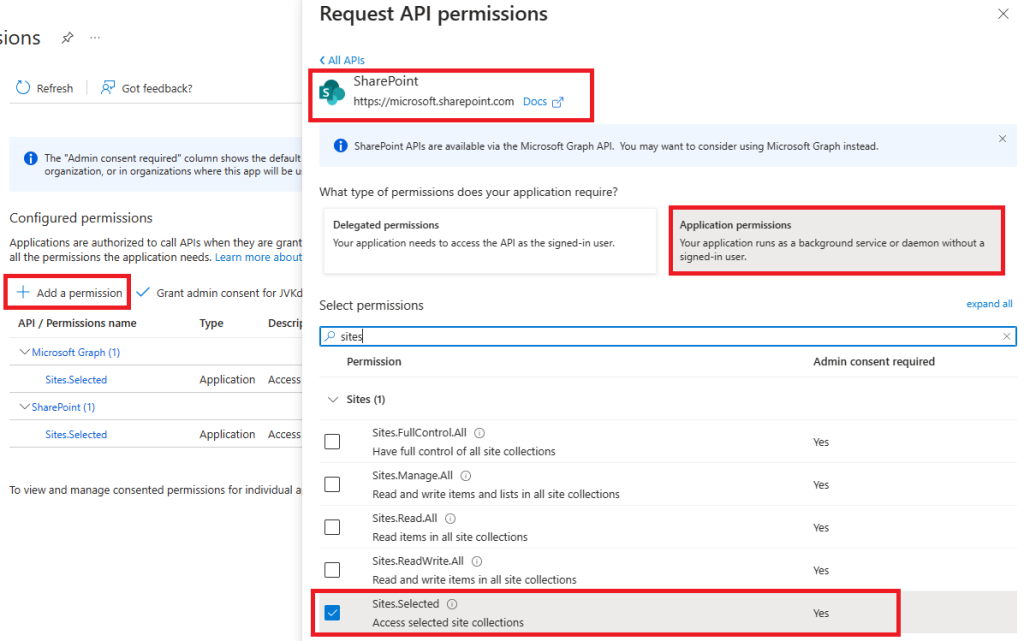
Provide or request tenant admin consent for your API permissions. Finally your app registration “API permissions” should look like:
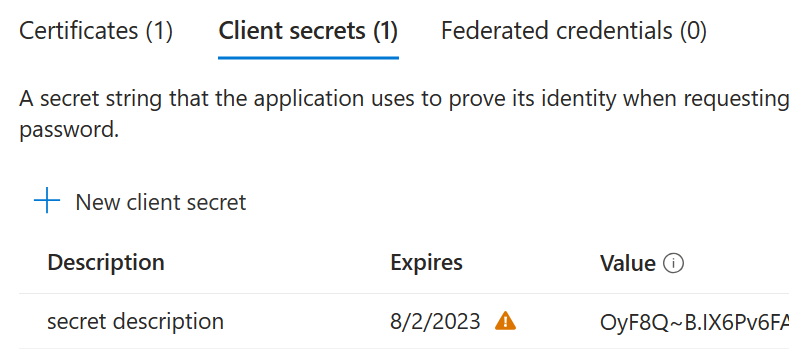
3. Under Certificates and secrets – generate client secret, copy secret value to safe location.
4. At the Overview page – grab your app client id and tenant id :
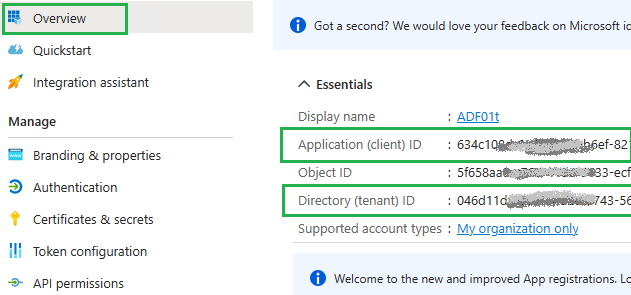
At this moment, having tenant id, app (client) id and client secret – you should be able to authenticate against Microsoft 365 tenant with app-only authentication path.
But! Having just Sites.Selected API permissions configured for app does not mean your app has access to SharePoint site. Access for the app to a specific site is provided by SharePoint team using PowerShell script or Graph API calls. That leads us to the next step.
5. Request access for the app to the SharePoint site (your SharePoint service admin should be able to do that via PowerShell script or Graph API calls )
– Here is the Graph API
– Here is PowerShell PNP cmdlet
Interesting that MS Graph advertises 3 possible roles – read, write and owner, but PNP team says you can select from 4 roles – Read, Write, Manage or FullControl.
Obviously, read role allows an app to read site content;
Write role is similar to “Contributor” user permissions – it allous CRUD operations agains list items (library documents and metadata), but does not allow create/update/delete or configure site lists/libraries or site itself. For this – you’d need Owner/Manage/FullControl role.
6. Once your SharePoint tenant/service admin confirmed that access has been provided – you can use app client id and client secret to work with SharePoint from your code using Graph API.
If any concerns – you can validate your app access to the target SharePoint site with simple PowerShell scripts: here is the sample code
7. Secure your certificate and/or secret
You do not hard-code secrets. Consider using vault to keep certificate/secret. If you host your application in Azure – consider using managed identity.
Note 1: Sites.Selected API permissions allows you call Microsoft Graph API with client Id and client secret. Calling SharePoint API with client secret is not supported. You have to use client id and certificate to call SharePoint API having app with Sites.Selected permissions.
Call SharePoint API with client Id and client secret is possible only if ACS-based permissions are provided for the app to the site, which is not recommended (see below).
Note 2: ACS-based permissions are going to be deprecated soon:
Your SharePoint admin doesn’t allow site owners to create/update ACS principal ⋆ Vladilen Microsoft 365 engineer
Update:
Microsoft announced decommissioning of ACS permissions. So do not use ACS for any new development.
It might be acceptable to provide ACS permissions for existing custom apps or 3-rd party or Microsoft apps/web apps (e.g. Alteryx, Azure Data factory) – apps that only support client id and secret and using SharePoint API under the hood – but just to not to break business processes and being aware of ACS EOL and planning a replacement of theses apps before 2026.
References
- Using AppRegNew (authenticate) and AppInv (authorize) for SharePoint app-only spns and ACS
- recent update to Microsoft 365 MC660075 that disables for site collection admins to create an Azure Access Control (ACS) principal via AppregNew
- Secret vs Certificate for Connecting to SharePoint Online programmatically
- SharePoint API vs MS Graph API
- how to provide ACS permissions for the application to SharePoint site.
Pingback: Automating Sites.Selected permissions provisioning ⋆ Vladilen Microsoft 365 engineer
Pingback: Microsoft Azure Data Factory connect to SharePoint ⋆ Vladilen Microsoft 365 engineer
Pingback: Providing ACS permissions for app to access SharePoint ⋆ Microsoft 365 engineering
Pingback: Your SharePoint tenant admin doesn't allow site collection admins... ⋆ Vladilen
One of the best and clear article which is to the point and explained the process . Topic and steps were furbished crisp and neat .