Being authenticated to Microsoft 365 tenant means Microsoft 365 knows who is trying to get access. To actually be able read/write or manage resource, your app must be Authorized to this resource.
For details – pls refer to MS authorization and Microsoft Graph API permissions. But again, in short in our case that means we need to have an API permission configured for our azure registered app. There are two kinds of API permissions – delegated and application.
Delegated permissions are intended to allow currently authenticated user to have access to the resource. Effective user permissions in this app would be an intersection of user own permissions and app permissions. So if an app have “Sites.FullControl.All” SharePoint delegated API permissions – that does not mean that user will have full control over all sites.
Here is an example of delegated permissions:
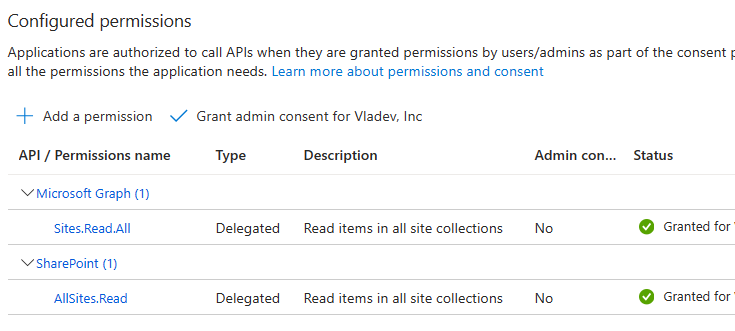
Permissions above allow you to search through SharePoint content being authenticated with your personal credentials. In search results you will see only content you already have access to.
Application permissions are what it says – once permissions are configured – application will have access to the resources according to API permissions.
Generally, application permissions allow an app to have access to all resources of the same kind in tenant, e.g. to get one specific groups owners an app must have “GroupMember.Read.All” permission that allows an app to read all tenant groups and their members. There are some exceptions – e.g. for Teams Microsoft developed RSC that allows scoped app access. For SharePoint there is a similar option – “Sites.Selected” API permissions.
API permissions must have an Admin consent. Here is an example of application permissions:
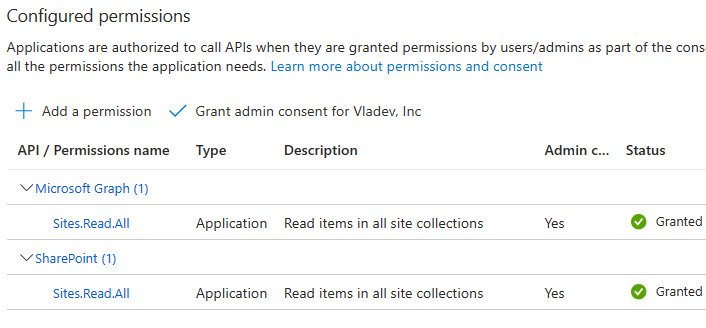
Permissions above allow your app to search all SharePoint content.
Pingback: Search Microsoft 365 content programmatically ⋆ Microsoft 365 engineering
Pingback: Using SharePoint REST API from Python code ⋆ Microsoft 365 engineering
Pingback: Get list of new m365 SharePoint sites or teams with PowerShell ⋆ Vladilen