Every resource under Microsoft 365 (Microsoft Teams team, Microsoft 365 group or SharePoint site) must have an owner/owners. Otherwise to whom we communicate on any question – site/group permissions, membership, site/group/team retention policy, content classification etc. Who will be responsible for team/site/group content and configuration and who will provide access to this site for other users.
NB. This article is about ownerless groups policy. There is a new (released 6.3.2025) “Site Ownership Policies” that can work against standalone sites.
MS: A team in Microsoft Teams or a Microsoft 365 group and its related services can become ownerless if an owner’s account is deleted or disabled in Microsoft 365. Groups and teams require an owner to add or remove members and change group settings.
Recently Microsoft implemented a new feature: a policy that automatically asks the most active members of an ownerless group or team if they’ll accept ownership. Very important feature. TY Microsoft!
It is important because many other “governance” activities (e.g. permissions attestation, retention policies) rely on site/team ownership. I.e., before we notify site owner that the site is going to be deleted due to inactivity – we want an owner present.
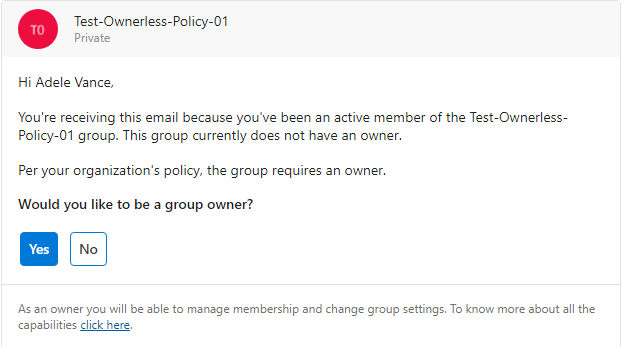
That is how the out-of-the-box notification email looks like:
The configuration via wizard is straightforward and intuitive, and Microsoft documented it well, but still we have some questions regarding the policy behavior.
Q: Is it about groups ownership or sites ownership?
A: Group ownership and group-based sites ownership (teams, yammer etc.). Non-group based aka Standalone sites (e.g. communication) are not in scope of this feature/policy.
Upd (June 2025): Microsoft released a new SharePoint “Site Ownership Policies” that works against standalone sites.
Q: Who can configure this policy? What kind of permissions required to create/update policy?
A: Microsoft says “Manage Microsoft 365 groups” permissions required – e.g. admins with Global admin or Groups Admin roles required. “Teams administrator” or “SharePoint Administrator” cannot configure the policy.
Q: After the policy activated – who will receive notification? What exactly “most active members” mean?
A: Microsoft only says “most active members” and does not disclose specific algorithm behind.
Q: How about group with no members? What if somebody created a group but did not add any members and then left?
A: In this case the policy will not work – as there is nobody who can be notified. These kind of groups must be handled manually, because having no owners or members does not mean that nobody uses the related SharePoint site. What if the group is public and hosts some valuable data?
Q: How do we know the group is ownerless? Only if owner has been deleted from AAD? What if an owner is just blocked or became unlicensed?
A: For the policy Microsoft consider blocked or unlicensed users presented in the group owners list as valid users and still group owners; so the policy will not be triggered until the group owners list is empty.
Q: We have implemented Azure AD Settings “EnableGroupCreation” and “GroupCreationAllowedGroupId” (as per Microsoft: Manage who can create Microsoft 365 Groups), so not everyone can create m365 groups. Would this impact the ownerless groups policy? In other words – if a user cannot create group – would this keep user from being assigned as a group owners?
A: No. Microsoft’s Manage who can create Microsoft 365 Groups trick regulates groups creation only. Later – when a group is created – nothing prevents such user to be added as a group owner.
Q: I support a large Microsoft 365 environment and we already have hundreds and thousands of ownerless groups. I’m concerned how users might react and whether our helpdesk support teams are ready for new type of tickets etc. Implementing the policy in test/stage environment does not make much sense, since there are no really active users etc. So, can I test this policy in production – on real users, but pilot it within a small number of users or ownerless groups before applying to all groups in the environment.
A: Yes, you can do a test or pilot implementation in production limiting the impacted users or groups.
– if you need to limit users who will be getting notifications – e.g. a “pilot team” – during Step 1 “Notification Options” under “Specify who can receive ownership notifications” you can select “Allow only certain active members” and under “Specify security groups to allow members” you can select a security group – so only members from the specified security group will be sent ownership request. Microsoft 365 groups do not work here.
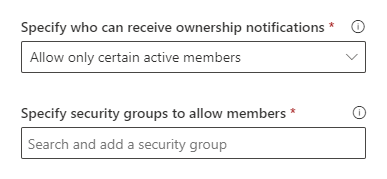
however – if you choose this option – it is possible that Microsoft 365 groups might have more active members who are not the security group members. E.g. it might make sense to use this option for piloting – against a small number of isolated set of groups/members, but for not for phased implementation. If you have some specific requirements for group ownership – e.g. “only managers could be group owners” or “contractors cannot be group owners” – using security group to limit potential group owners would make sense.
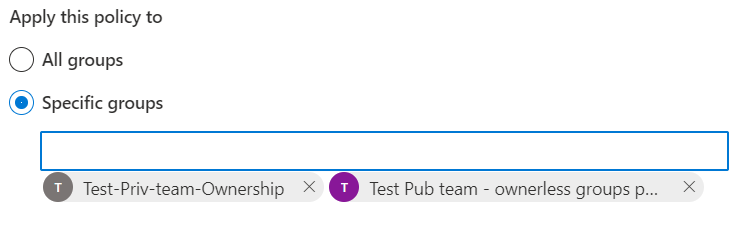
Another option you can use for phased implementation or piloting the policy is to scope it down to a several selected m365 groups – use “Apply policy to” – “Specific groups” option:
NB! After all notifications are sent for a group – you will never ever get any more notifications for the same group. Even if you re-activate the policy or change policy parameters or whatever – it will not help. Once messages sent – it’s done for the group forever.
NB: Please also check “Microsoft ownerless groups policy in large environment“
Q: How many groups I can specify if I select Apply policy to Specific groups option? Is there a maximum?
A: Yes, there is a limit. You can specify no more than 50 groups.
Q: I know the policy is applied to Microsoft 365 groups only. But I have many standalone sites with no owners (no site collection administrators). How do I deal with ownerless SharePoint sites?
A: Options are: manual intervention, PowerShell, 3-rd party tools – depending on your specific case. E.g. you can elevate some “Site Owners” SharePoint group members to site administrators. For modern sites – how about converting standalone sites to Microsoft 365 group-based sites (TBC – as at the moment it is not clear if it is possible)?
Q: What happens after one of the notified members accepts the ownership request?
A: No more notifications will be sent for this group. But previously sent notifications will still be valid.
Q: What happens if several of the notified members accepts the ownership request?
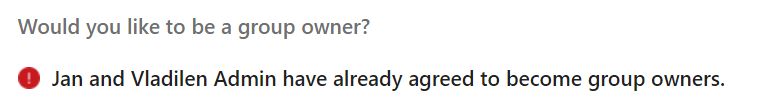
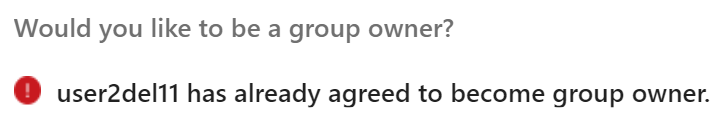
A: Only two first served basis. As per Microsoft, only two members can be assigned to group owners via the policy. When a group got two owners – invitation message actionable item for the rest will be converted from “Would you like to be a group owner?” to “MemberName1 and MemberName2 have already agreed to become group owners.” with no “Yes” and “No” actionable buttons.
NB!
I have tested the policy one more time, and this time after first member accepted ownership – no other members were able to accept ownership. They got a message “Johan Lorenz has already agreed to become group owner”:
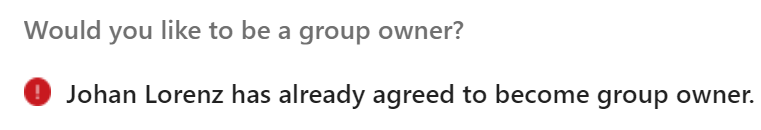
@Microsoft, any comments?
Q: What if admin assign owner to group?
A: The group becomes not ownerless. Notification messages will not display invitation to become an owner anymore, and instead of “Would you like to be a group owner? – Yes or No buttons” it will be shown as “username has already agreed to become group owner.”:
Q: Can I customize an ownership notification?
A: Yes, but
– E-mail message body is limited to ~1040 characters
– Policy does not provide any WYSIWYG rich text format options (but there are some tricks you can use to format it with headers, bold/italic, links, bullets/lists: more on email template format.)
Q: Can I use shared mailbox or security group or distribution list as a “send from” e-mail account?
A: No. You can use only user or m365 group mailbox.
Q: Should “send from” user e-mail account be licensed with Exchange?
A: TBD (but most likely no).
Q: What if a group become ownerless after policy is activated?
A: Policy detects the group is ownerless and start sending notifications within 24 hour.
Actually the policy was designed to prevent ownerless groups. So it is recommended to activate the policy once you get the tenant.
Q: We know, that if a user declined ownership once – he will not get any more emails on the same. Is that true for current policy or for any further policies activations? I.e. If the policy updated/re-activated – will it remember user’s decision or it all starts from scratch?
A: TBD
All the next incarnations of the policy will not trigger e-mail notification for the group if all notifications were sent earlier. I.e. in this case user will not receive any more notifications on the same group.
Q: If a user declines ownership – does that mean that someone else will start receiving emails so that the configured number of active members is maintained? What if all “active members” choose “No” at week 1 – will the policy select other members or what?
A: No. The policy will send notification to other initially selected members.
Q: If nobody accepted ownership – can we reconfigure the policy to sent more notifications – e.g. to wider range of active members or with more strict language in an e-mail template?
A: Yes and No.
Yes – if you e.g. specified 2 members and 6 weeks in the policy, and then after 3 weeks you want to increase number of members to notify to 10. But (it seems like it’s a bug) you have to deactivate the policy and activate it again with new parameters.
No – if the policy’s specified number of notifications is expired. I.e. if all emails supposed to be sent are sent – no more emails will be generated for this group, even if you reconfigure or deactivate/activate the policy, so the group active members will not get any more notifications on the same group. Workaround: you can add a dummy account to group owners and then delete this dummy account from AAD, so groups become normal and then ownerless again.
Q: What if we specify emails should be sent for 5 weeks, but stop the policy after two weeks? And then we re-activate the policy.
A: It is expected the policy will continue sending e-mail notifications until 5 emails sent.
Q: What if we specify 3 weeks in policy, but then re-configure the policy with 5 weeks specified and activate it again?
A: tbc – not tested yet
Q: Is there a difference in the policy behavior when we reconfigure the policy or deactivate and then reconfigure the policy?
A: Yes, at least – what I noticed so far:
To update number of members to notify – if you just reconfig the policy – it pics up update but acts like there was no updates. So to actually update number of members to notify you need to deactivate the policy and activate it again with new parameters.
Q: What if we have more than 10,000 notifications to send? Will the policy drop some of them or all notifications will be send but next day?
A: tbc – not tested yet
Q: Let say we have an ownerless group with 20 members. Let say we specified security group to limit user who will get invitations. And this security group includes only 6 users from the orphan group out of total 20. Microsoft says the policy will select the most active users. So the question is: will the policy select the most active users from the 20 orphaned group users and if the user in the security group – he/she will get an email?
A: No. The policy will select the most active users only from these 6 users that included in the security group, ignoring 14 users, even if they were more active then these 6 selected.
Q: What happens after the policy expires? E.g. after all notifications are sent…
A: Policy does not expire. If the policy is activated – it works. If all notifications are sent for the group – so yes, policy is done for this group. But if a new group became ownerless – policy will be triggered for this group again.
Q: If all the notifications are sent for the group – what are admin options to activate ownerless groups policy against this group?
A: There are no “legal” options, but there is a workaround. You can add an owner to the group and then delete this account – so this way you make the group ownerless again – and the process would start from scratch, as for the policy this group will be a new ownerless group.
Some more findings:
User can forward invitation message, but recipient who is not a selected group member – will not see actionable “Yes” “No” buttons. Selected Group
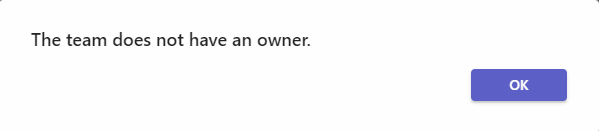
If a public group does not have an owner – all requests to joint the team will be declined with “The team does not have an owner” message:
(that means no new members, i.e. no new contributors, but read-only visitors access is still available for everyone, as group is public):
Users can go to My Groups to see groups (Teams, Yammer communities and SharePoint Sites) they are members or owners of.
Proposal to be a group owner lasts forever. So if a user after some time finds an email that asks him “Would you like to be a group owner?” and clicks Yes – he/she will be a group owner, even if the policy is already updated or removed.
As per Microsoft, only first two members can accept the ownership of an ownerless group. No additional members are allowed to accept ownership. If either one or two members accept ownership, other members won’t receive further notifications.
Re-create (or re-activate) the ownerless group policy
You can de-activate the policy and then activate it again. Or you can reconfigure the policy. If you activated the policy again (or re-configured it), but emails are not sent – this might be an expected behavior. Let say you initially specified 3 weeks and 3 notification were sent to the most active ownerless groups members. That means no more emails will be generated for these groups.
De-activate the ownerless group policy
Just uncheck “When there’s no owner…”, and save it to stop the policy:
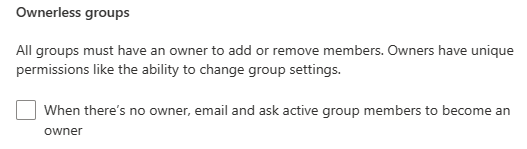
downside – you’d need to configure the policy from scratch – all previous settings are gone now
Track the ownerless group policy in action via Audit Log
How do I, as an Microsoft 365 administrator, know if the policy works or not, are the emails sent or not and how many (if any) users are accepted “Would you like to be a group owner?” invitation?
Microsoft 365 Audit Search under Microsoft Purview (Compliance center) should help.
Operations:
- OwnerlessGroupNotified – “Notified ownerless group”
- OwnerlessGroupNotificationResponse – “Responded to ownerless group notification”
- OwnerlessGroupNeedAttention – “Unattended ownerless group”
OwnerlessGroupNotified – “Notified ownerless group”
(No-brainer) – means that the policy sent e-mail notification to some of the group members. Under “Members” property you can see list of notified users, and under ExtendedProperties – “FirstNotificationDate” and “NotificationChannel” (usually “Outlook”)
OwnerlessGroupNotificationResponse – “Responded to ownerless group notification”
Could have “ResponseType” as “AcceptOwnership” or “DeclineOwnership” under ExtendedProperties, as well as “OwnerCount”.
OwnerlessGroupNeedAttention – “Unattended ownerless group”
indicates all notifications are sent and the group is still ownerless. In the event details you’ll find under ExtendedProperties:
{
"Name": "FirstNotificationDate",
"Value": "05/04/2023 13:46:07"
},
{
"Name": "LastNotificationDate",
"Value": "05/11/2023 14:28:21"
},
...UserId: OwnerlessGroupComplianceAssistant
Record Type (AuditLogRecordType): 126
It seems like event is not added to the Audit log when a policy is created or updated.
Who can create Microsoft 365 Groups
It is possible to limit users – who can create Microsoft 365 Groups (please refer to Microsoft: Manage who can create Microsoft 365 Groups – there is a guide and PowerShell code sample). This might help to keep the environment under control – let say, “only managers can create groups”, or “contractor should not be able to create teams”.
Azure AD Directory Setting “GroupCreationAllowedGroupId” works only for creation. Later, when the group is create – it is possible to add to group as a group owner those who is not able to create group. But, if you want your tenant configuration consistent in terms “if a user cannot create a group – user cannot be a group owner” – consider using the same security group in policy’s notofication options “Specify who can recieve ownership notifications”
Issues
“Ownerless group policy configuration failed” error message.
And “Failure in configuring ownerless groups policy” and “Please try again.”
– seems like a permissions issue.
SharePoint admin, Teams admin or Group admin roles: cannot configure Ownerless Groups Policy.
Global admin: yes, can configure Ownerless Microsoft 365 Groups Policy.
What is the minimum role required?
According to a recent update of the Microsoft’s article – “A Global administrator can create a policy…”. In my experience – groups admin can also configure the policy.
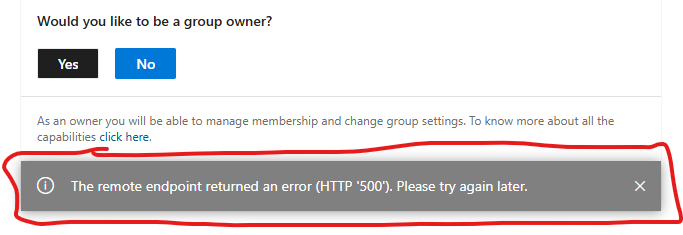
The remote endpoint returned an error (HTTP ‘500’). Please try again later
When a user clicks on a button “Yes” or “No” in a notification email, a message “The remote endpoint returned an error (HTTP ‘500’). Please try again later.” pops up:
We are unable to complete that action right now
Since around Feb 5 2025 users who want to accept group ownership and click Yes – get an error message “We are unable to complete that action right now.Please try again later.”
Microsoft is aware of it. Waiting for a fix.
Update: this bug was fixed by Microsoft in a few weeks/months 🙂
References
- Microsoft: Manage ownerless Microsoft 365 groups and teams
- Microsoft: Microsoft 365 ownerless group policy
- Microsoft: Manage who can create Microsoft 365 Groups
- Vladilen: Ownerless groups in Microsoft 365 tenant all articles (index)
- Video Tutorials: Microsoft 365 ownerless groups policy deep dive
- Vladilen: “Site Ownership Policies deep dive”