How do we know when the SharePoint site was last updated?
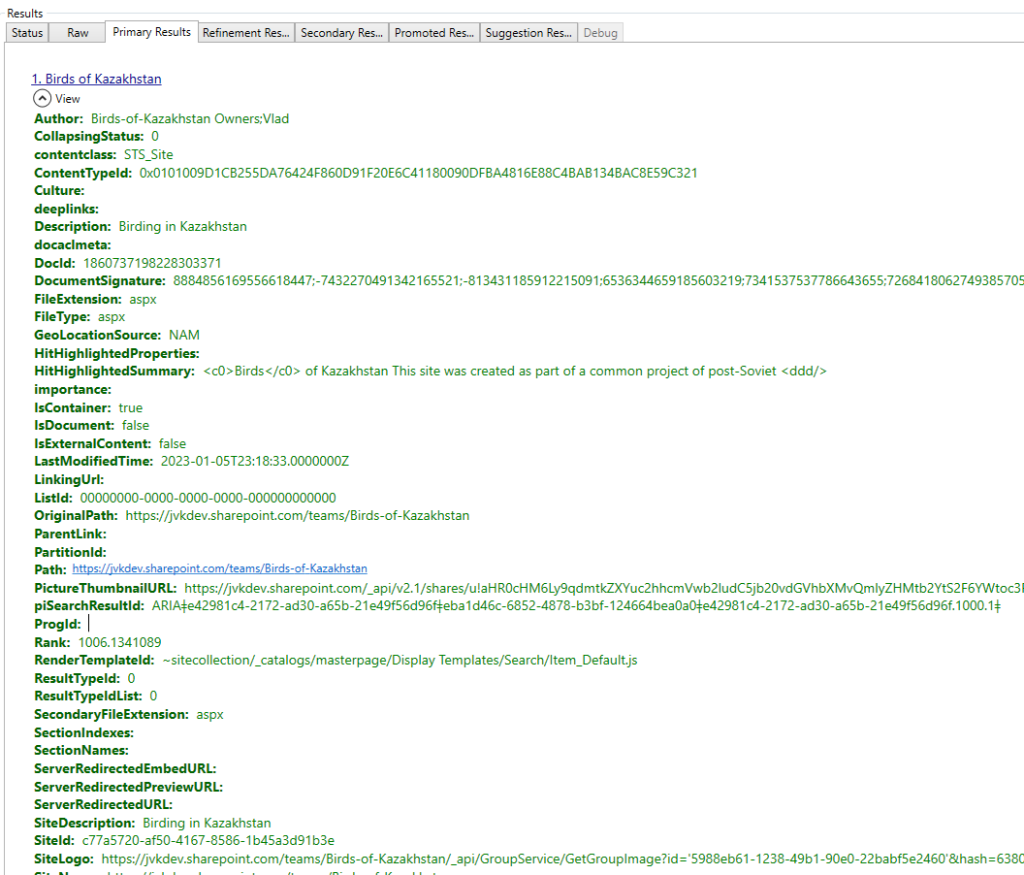
We have multiple “when the site was modified last time” properties – e.g. some we can retrieve with SharePoint CSOM:
- Site LastContentModifiedDate
- Web LastItemModifiedDate
- Web LastItemUserModifiedDate
Also we can get
- MS Graph site object with LastModifiedDateTime property
- get usage reports via Microsoft Graph (activity reports), and
- use “Last activity” field via Admin Center GUI
On the other hand – we can view and modify site in multiple ways – visit site home page, open and/or update document/list item, change site/library settings, configure site permissions, assign site sensitivity label, setup site property and so on.
Question: which site “last modified” or “last activity” properties reflect what events/actions?
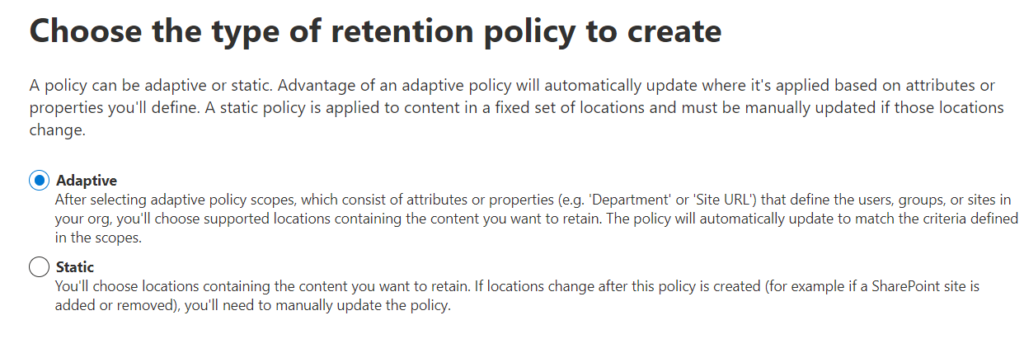
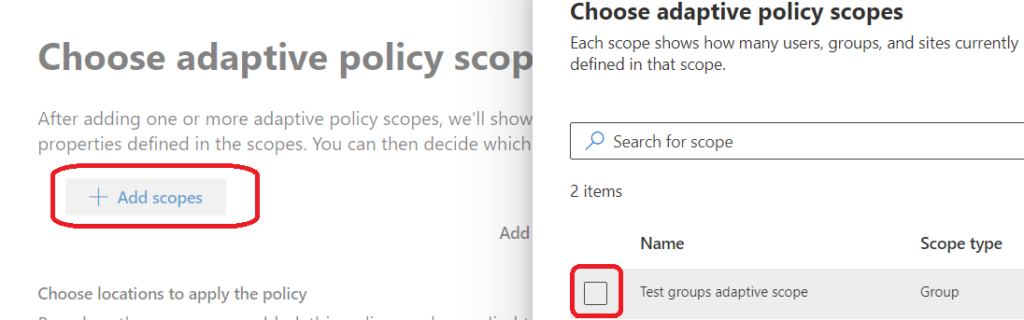
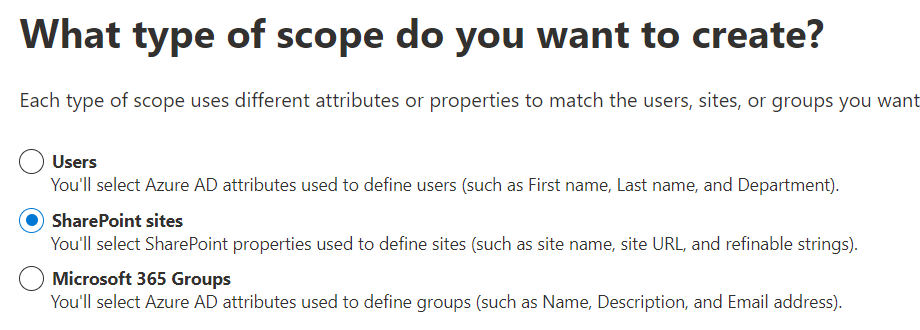
This might be important if we think of retention policies, or any kind of clean-up processes… Let say, we are getting report on abandoned sites (inactive sites), but we are also assigning sites sensitivity labels, or we are updating site custom properties (e.g. for adaptive scopes), we have an ownerless groups policy working etc.
What if we assign site sensitivity label to an old inactive (5 years old) site – would it affect retention policy since site was updated this way?
Results
So i did some tests and based on detailed results below, it seems like
- Web LastItemModifiedDate is triggered when user just visited site (but property LastItemUserModifiedDate is not triggered)
- If a document or list Item updated by user or app – all properties are triggered
- MS Graph site property LastModifiedDateTime, root web property LastItemModifiedDate and Site LastContentModifiedDate – same values
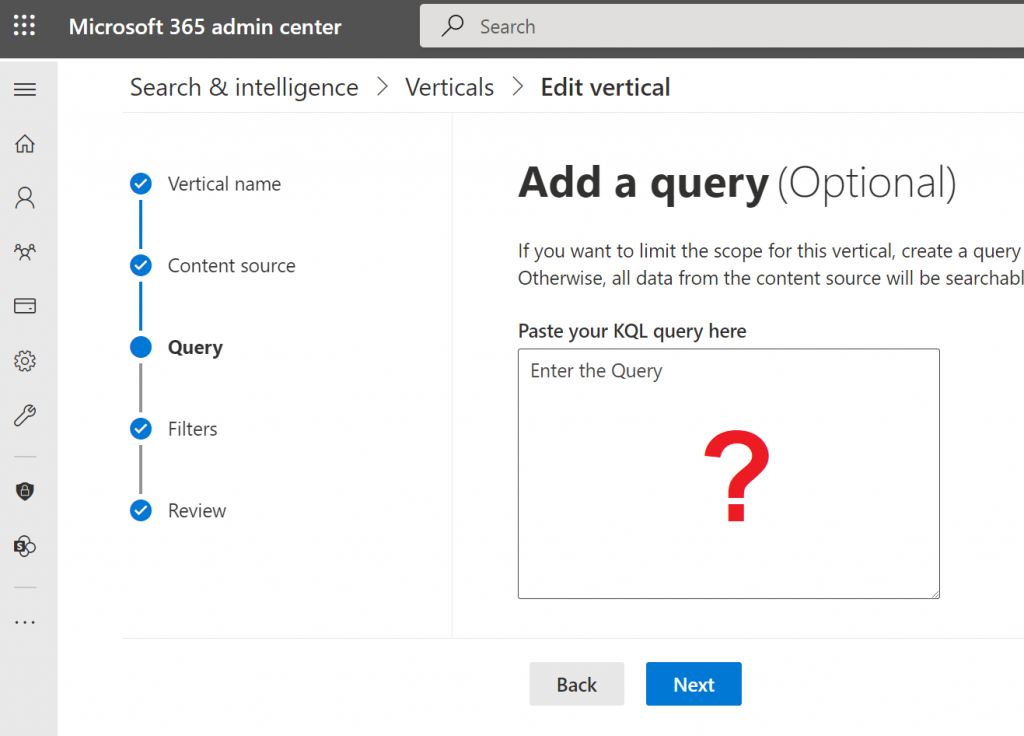
- If site custom property is updated – it does not affect any site “last modified” property
- The same for sensitivity label updated by app – it does not affect any site “last modified” property
- The same for Microsoft ownerless groups policy – when user accept or decline group membership – no site “last modified” properties are changed (the same is true for Microsoft 365 group last modified date/time property).
Please refer to the table below
Detailed test results
Test results if the event triggers property update:
| Event | Last Content Modified Date | Last Item Modified Date | Last Item User Modified Date | Graph Last Modified DateTime | GUI Last activity |
| Page viewed by user | Yes | Yes | No | Yes | |
| Home Page viewed by user | |||||
| Site Page viewed by user | |||||
| Document or list item updated by user | Yes | Yes | Yes | Yes | |
| Document or list item updated by app | Yes | Yes | Yes | Yes | |
| Site config settings updated by user | |||||
| Site config settings updated by app | |||||
| Site custom property updated by app | No | No | No | No | |
| Site Sensitivity label updated by user via SharePoint | Yes | No | No | No | |
| Site/Group Sensitivity label updated by user via Teams | |||||
| Site/Group Sensitivity label updated by user via Azure | No | No | No | No | |
| Site Sensitivity label updated by app | No | No | No | No | |
| Site collection admin updated by user | Yes | Yes | No | Yes | |
| Site collection admin updated by app | Yes | Yes | No | Yes | |
| SharePoint group membership updated by user | Yes | Yes | No | Yes | |
| Standalone Site connected to a group by user | Yes | Yes | Yes | Yes | |
| Add Microsoft Teams to Site by User | Yes | Yes | Yes | Yes | |
| Update m365 group membership via M365 admin console by admin | Yes | Yes | No | Yes | |
| Update m365 group membership via Azure by admin | |||||
| Update m365 group membership via Teams by user | No | No | No | Yes | |
| Update m365 group membership via App | |||||
| Accept group ownership invitation sent by ownerless groups policy | No | No | No | No | |
| Decline group ownership invitation sent by ownerless groups policy | No | No | No | No | |