There has always been one problem in the SharePoint world: full site permissions report. Full means across entire site – including all objects with broken permissions.
It seems like Microsoft has solved the problem: Full site permissions report is available for site owners out-of-the-box.
How to get SharePoint All Site Permissions Report
(Ensure you are site collection admin or team/group owner).
Just navigate to Site Usage, scroll to the end and run report.
- Select gearbox “Settings” and then Site usage:

Or Select “Site Contents”, then “Site Usage” as shown below:

2. Scroll down to the “Shared with external users” block and click “Run report”:

- Create/Select folder (*) for the report and click “Save”:
- If there are no folders in the Documents folder – you need to create one (otherwise you will not be able to save it:)

- Once yo have a folder available – just click “Save”:
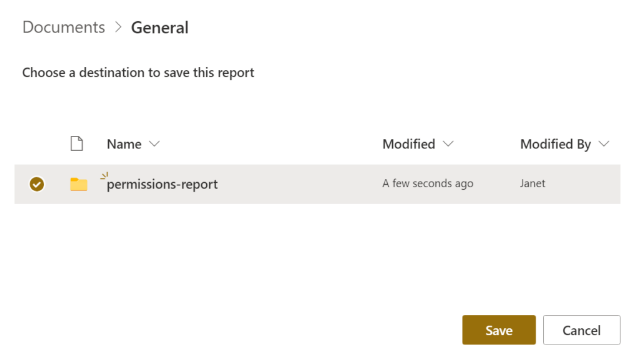
Give it some time (5-10 minutes) – check the folder’s content. There should be a file with a report on all site permissions.
For items shared with direct access, the report contains one row for each user / item combination.
SharePoint groups are shown in the report as groups (not individual users inside them… so you have to check group membership to get really full permissions report).
Again, you must be a site admin to run the report.
- Secure the permissions report
If you don’t want other site members to see the report – secure the report’s folder – e.g. for site owners and for those who must be able see the report…
Consider creating a separate library for permissions reports and secure it instead of securing a folder under Documents.
Some more ideas on SharePoint permissions
Permissions are tricky in SharePoint. By default, you have permissions assigned to the root site of the site collection and all subsites, libraries etc. inherit root permissions.
But you can break inheritance at any level you need to provide specific (unique) permissions to the resource.
Of course you can always navigate to the resource and check resource permissions. But… what if there are hundreds of broken permissions… should you iterate everything under your site to check manually if permissions are broken or inherited?
So the real problem was – you never knew who have access to your site as there was no out-of-the-box tool to get all site permissions in one single report. There are third-party solutions – like ShareGate, Metalogix or SysKit – or you can develop PowerShell script generating report on all SPO site permissions. But… finally Microsoft solved this problem – Microsoft implemented out of the box full site permissions report.
Reference:
Microsoft Report on file and folder sharing in a SharePoint site